In Part 1, we created the Kubernetes cluster by running kubeadm init on the control plane node. In part 2 we’ll add a node to an existing cluster that will be capable of running pods which is apparently a possible CKA exam scenario (see cluster ik8s):

The basic requirements for a Kubernetes node found in the installing kubeadm doc are relevant for any node you’re adding to a Kubernetes cluster; whether that is a control plane or regular node. For the exam, I don’t think this level of detail will be required but still important to know!
Getting a kubeadm Bootstrap Token
To join a Kubernetes cluster created with kubeadm, we need a join token. Immediately after a new cluster is created, a join token is automatically created. We can use that if the node is being after the control plane is setup. But the initial join token expires after 24 hours! So how do we get a join token for new nodes if it’s been longer than 24 hours?
Create a New kubeadm Join Token
The kubeadm token create command creates a new join token but that’s not everything needed to join the cluster. We also need the –-discovery-token-ca-cert-hash. Fun..where do we get that?! I wouldn’t have a clue without the --print-join-command parameter that outputs the full join command which includes the discovery-token-ca-cert-hash:
ubuntu@controlplane01:~$ kubeadm token create --print-join-command
kubeadm join 192.168.1.117:6443 --token bfjdln.n6hc9k0ksgqp5gul --discovery-token-ca-cert-hash sha256:9280809027de3ccdbdedd68ce3b0f63e38f67e763c78c81078a8c52a68dd527cAdding the Node to Kubernetes Cluster
Now that we created a kubeadm join token, let’s use it to add a node to the cluster:
ubuntu@node-02:~$ sudo kubeadm join 192.168.1.117:6443 --token bfjdln.n6hc9k0ksgqp5gul --discovery-token-ca-cert-hash sha256:9280809027de3ccdbdedd68ce3b0f63e38f67e763c78c81078a8c52a68dd527c [preflight] Running pre-flight checks
[WARNING IsDockerSystemdCheck]: detected "cgroupfs" as the Docker cgroup driver. The recommended driver is "systemd". Please follow the guide at https://kubernetes.io/docs/setup/cri/
[preflight] Reading configuration from the cluster...
[preflight] FYI: You can look at this config file with 'kubectl -n kube-system get cm kubeadm-config -oyaml'
[kubelet-start] Writing kubelet configuration to file "/var/lib/kubelet/config.yaml"
[kubelet-start] Writing kubelet environment file with flags to file "/var/lib/kubelet/kubeadm-flags.env"
[kubelet-start] Starting the kubelet
[kubelet-start] Waiting for the kubelet to perform the TLS Bootstrap...
This node has joined the cluster:
* Certificate signing request was sent to apiserver and a response was received.
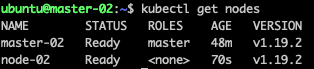
* The Kubelet was informed of the new secure connection details. Run 'kubectl get nodes' on the control-plane to see this node join the cluster.Once complete, we can verify from kubectl get nodes on the control plane node:
Finally, let’s schedule a pod and see it:
ubuntu@controlplane01:~$ kubectl run nginx --image nginxpod/nginx created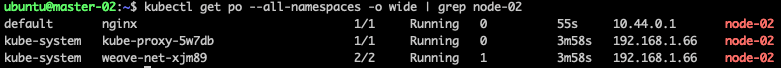
Success! The nginx pod we created is running on node-02 along with kube-proxy and weave-net pods that were scheduled on the node when it joined the cluster.
Questions or comments? Reach out to me on Twitter or LinkedIn!


Pingback: CKA 2020 Curriculum for Kubernetes v1.19 | Brandon Willmott